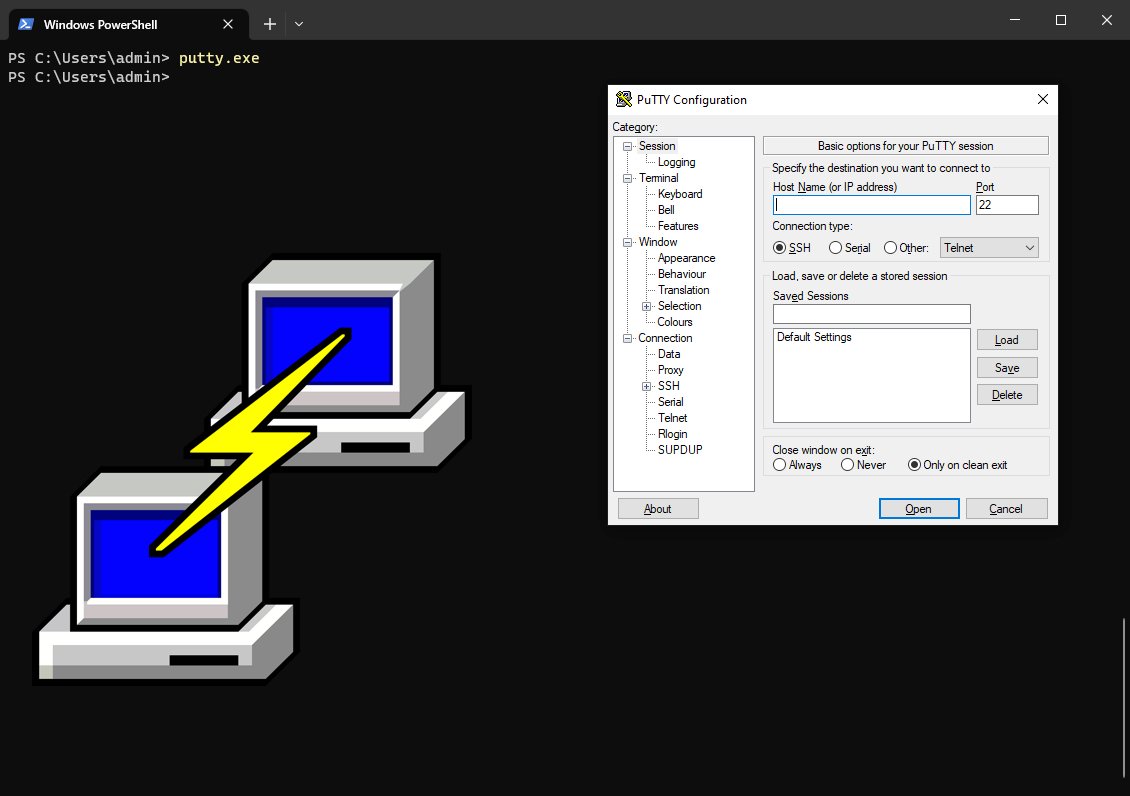
How to Download & Install PuTTY On Windows
PuTTY is an SSH and telnet client that has been widely used in the realm of remote connectivity and secure communication since it’s initial release in 1999. The PuTTY tool is available to download through the web, Microsoft Windows App Store, as well as through the Windows Package Manager (WinGet). In this article we will use modern methods to download and install PuTTY as well as explore the key features and components that simplify the task of connecting to remote servers while prioritizing data security. With its ease of use and plethora of applications including secure data transmission PuTTY has long solidified itself as a staple in the toolkit of anyone who seeks seamless and secure communication in today's interconnected digital landscape.
How to Install the YARA Malware Analysis Tool On Windows
YARA is an indispensable tool designed to identify malware, malicious, and suspicious elements based on defined patterns. YARA rules are text-based patterns that describe characteristics of files, such as specific byte sequences, strings, regular expressions, and more. In this comprehensive guide, we will delve into the step-by-step process of installing YARA on the Windows operating system. By the end of this tutorial, you'll have a clear understanding of how to harness YARA's capabilities to create custom rules, scan files and directories, and fortify your system's defenses against potential cyber threats.
SSHFS On Windows: How To Use
Learn to leverage SSH Filesystem (SSHFS) on Microsoft Windows devices with this comprehensive guide. While our previous blog covered SSHFS usage on MacOS, this article shifts the spotlight to Windows. Discover the power of SSHFS for seamlessly mounting remote drives from Windows, Linux machines, and top cloud platforms like Amazon Web Services (AWS), Microsoft Azure, and Google Cloud. With SSHFS, data transmission occurs via the secure SSH protocol, utilizing TCP connection over port 22 to ensure dependable and efficient data transfer. Elevate your cross-device and cross-cloud file management with SSHFS.
How To Use SSH on Windows
In this article I’m going to show you can use SSH on Windows machines. We’ll go over the installation of OpenSS, basic SSH configuration, as well as connecting to and from a Windows and Linux machine.
The Secure Shell (SSH) Protocol is a network protocol that allows secure access to interact with remote network resources over port 22. SSH is commonly used for remote login and command-line execution for administrative purposes. Microsoft Windows uses an implementation of OpenSSH to implement the SSH protocol and actively maintains this software project on GitHub under the openssh-portable repository.
Sudo in PowerShell: Get Administrator Privileges With gsudo
Are you tired of having to right click run “Run as administrator” in order to get an elevated PowerShell terminal? Wouldn’t it be nice to elevate the current Windows shell in a simple way? We are all familiar with the Linux sudo command but did you know there’s an awesome Windows equivalent in gsudo! In this tutorial I’m going to show you how to install and configure this awesome Windows application.
How To Install Windows 10 on VMware Fusion
In this post I’m going to show you how to setup a Windows 10 virtual machine in VMware Fusion. We’ll cover where to download the Windows 10 ISO from Microsoft, how to import ISO’s, how to configure hardware such network adapter, CPU’s, RAM, how to install Windows 10 on VMWare Fusion, as well as some tips and tricks for post installation. For those unfamiliar Fusion is the MacOS software hypervisor developed by VMware. If you’re on a Windows Machine you’ll be using VMware Workstation which is the software hypervisor for Microsoft Windows.
How To Use Windows Package Manager (WinGet) Tool
Windows Package Manager (winget) is a package manager specific to the Windows operating system. Winget is similar to what many Linux users are already familiar with options such as the apt and yum package managers. For those unfamiliar, a package manager allows system users the ability to install, upgrade, configure, and remove software efficiently using a program specifically tailored to handle these operations. In this post I will help you install winget, verify, get help, install, upgrade, and uninstall packages using this underutilized Windows utility.
Exploring Defense Evasion through Reflective Code Loading (T1620)
Reflective Code Loading, identified as T1620 within the MITRE ATT&CK matrix continues to be a prevalent defense evasion technique frequently encountered during routine threat hunting activities. It notably attains popularity in the context of loading .NET assemblies within the Windows operating system. This technique can be employed by threat actors to load numerous amounts of malicious software including, malware, ransomware, and exploits against known software vulnerabilities.
How To Make HTTP/HTTPS Web Requests in Rust
In this blog post I will show you how to make web requests in Rust using the Reqwest and Hyper crates. Using web requests forms the basis of interacting with many different services such as API’s, AI services, web-servers, microservices, and other connected devices such as IoT devices. Since many of the core features of modern interconnected devices rely on web requests this makes it critical for programmers to understand, implement, and troubleshoot it’s functionality in an increasingly connected world.
Decrypt Traffic with Mitmproxy & Wireshark
In some situations during your career as a security researcher or another area under the cybersecurity umbrella one may need the capability of decrypting application layer traffic such as HTTPS and WebSockets.
To decrypt HTTPS or WebSockets traffic, we can utilize mitmproxy to decrypt SSL/TLS and Wireshark to analyze that traffic. From a security context, we are essentially creating a man-in-the-middle condition locally.
How To Use SSHFS on macOS
Using sshfs is a great way to mount a remote drive from AWS, Azure, or any remote machine to your local mac. Installing sshfs is a relatively straightforward process.